Sitecore XP on AWS
Partner Solution Deployment Guide

April 2022
Tony Bulding, Sasidhar Reddy Bhumireddy, and Borja Prado, AWS Integration & Automation team

| Refer to the GitHub repository to view source files, report bugs, submit feature ideas, and post feedback about this Partner Solution. To comment on the documentation, refer to Feedback. |
This Partner Solution was created by Amazon Web Services (AWS). Partner Solutions are automated reference deployments that help people deploy popular technologies on AWS according to AWS best practices. If you’re unfamiliar with AWS Partner Solutions, refer to the AWS Partner Solution General Information Guide.
Overview
This Partner Solution deploys Sitecore XP on the AWS Cloud. If you are unfamiliar with AWS Partner Solutions, we recommend that you read the AWS Partner Solution General Information Guide.
Costs and licenses
This Partner Solution requires a Sitecore XP license. To use the Partner Solution in your production environment, sign up for a developer trial license. For a full license, contact a Sitecore sales representative or Sitecore partner. Before you launch the Partner Solution, place the license key in the deployment’s associated S3 bucket, and specify its location. For more information, see the Pre deployment steps section.
If you don’t have a license, the Partner Solution deployment will not complete successfully.
There is no cost to use this Partner Solution, however you will be billed for the resources deployed. For more information see the AWS Partner Solution General Information Guide.
Architecture
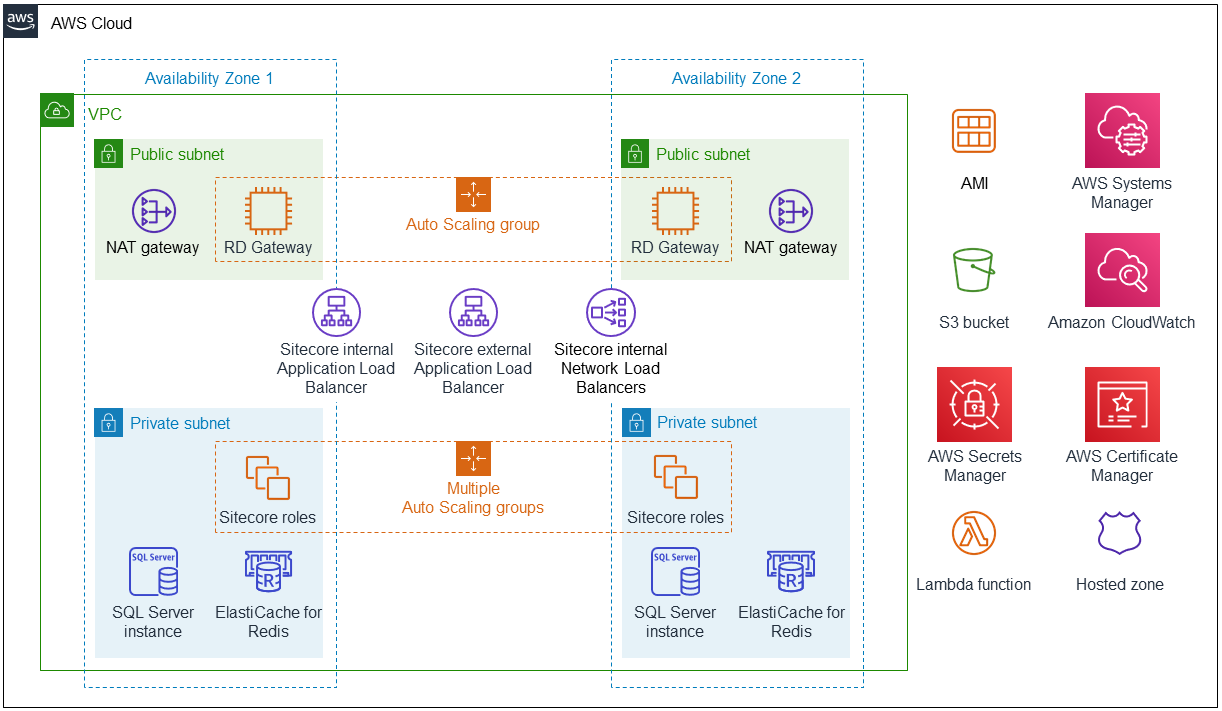
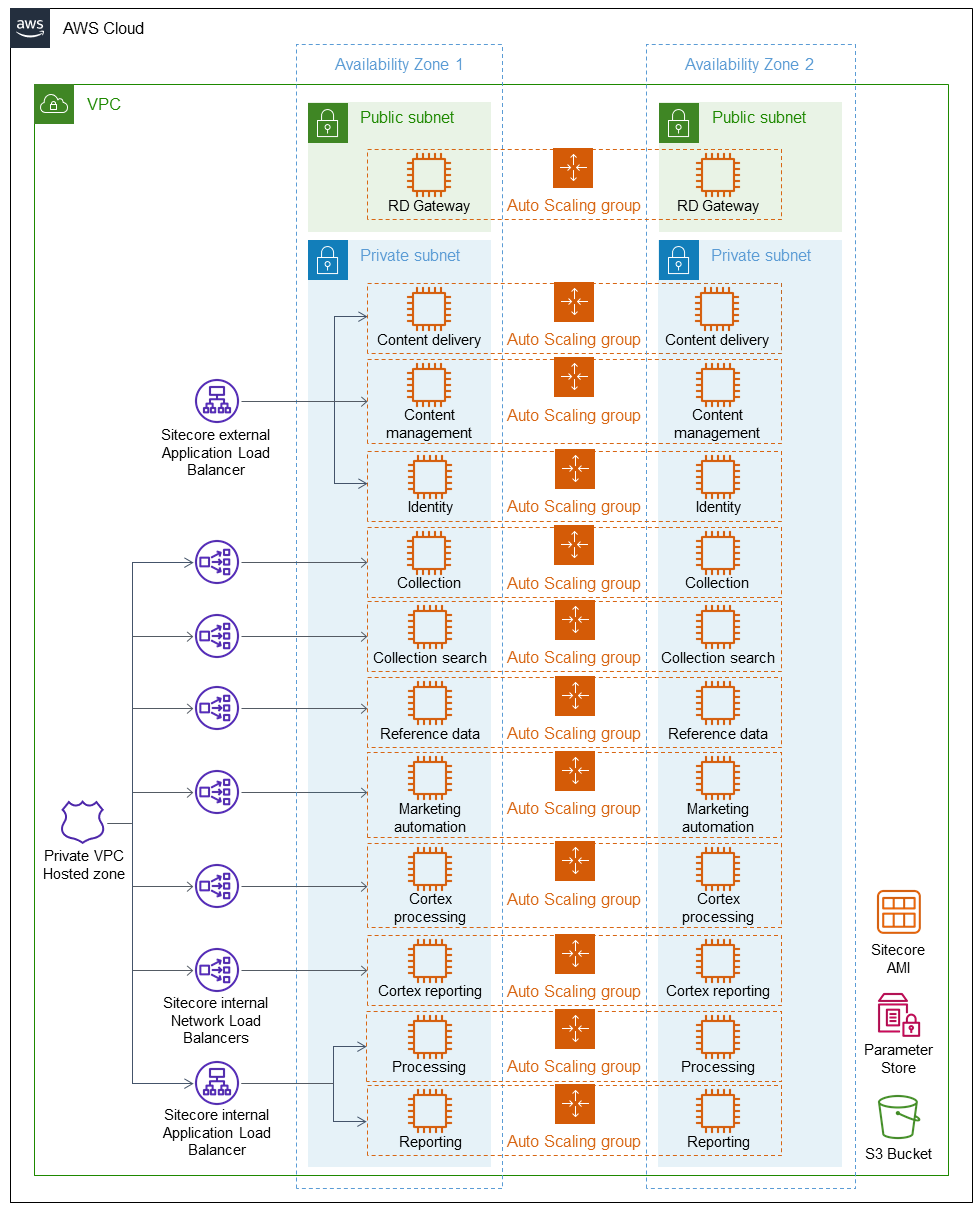
Deploying this Partner Solution for a new virtual private cloud (VPC) with default parameters builds the following Sitecore environment in the AWS Cloud.
As shown in figures 1 and 2, the Partner Solution sets up the following:
The Partner Solution sets up the following:
-
A highly available architecture that spans two Availability Zones.*
-
A virtual private cloud (VPC) configured with public and private subnets, according to AWS best practices, to provide you with your own virtual network on AWS.*
-
In the public subnets:
-
Managed network address translation (NAT) gateways to allow outbound internet access for resources in the private subnets.*
-
Microsoft Remote Desktop Gateway (RD Gateway) instances in an Auto Scaling group. This provides inbound remote desktop access to Amazon Elastic Compute Cloud (Amazon EC2) instances in the public and private subnets.*
-
-
An internal Application Load Balancer to route traffic to Sitecore reporting and processing instances.
-
An external Application Load Balancer for routing traffic to Sitecore content and identity role instances.
-
Network Load Balancers for Transport Layer Security (TLS) pass-through to the remaining Sitecore instances.
-
In the private subnets:
-
Sitecore roles deployed on Amazon EC2 instances. Each role is deployed to one EC2 instance, and each instance is deployed to an Auto Scaling group.
-
Amazon RDS SQL Server instances.
-
Amazon ElastiCache for Redis for cache management.
-
-
An EC2 Amazon Machine Image (AMI) for the initial deployment of Sitecore roles and subsequent Auto Scaling events.
-
AWS Systems Manager to store parameter data and the AMI automation build document.
-
An Amazon Simple Storage Service (Amazon S3) bucket for storing static data.
-
Amazon CloudWatch for monitoring deployed services.
-
AWS Secrets Manager and AWS Certificate Manager (ACM) for access control.
-
A Lambda function to convert and import the Sitecore client certificate into ACM.
-
An Amazon Route 53 private hosted zone for internal Domain Name System (DNS) lookups within the VPC.
* The template that deploys the Partner Solution into an existing VPC skips the components marked by asterisks and prompts you for your existing VPC configuration.
Deployment options
This Partner Solution provides two deployment options:
-
Deploy Sitecore into a new VPC. This option builds a new AWS environment consisting of the VPC, subnets, NAT gateways, security groups, bastion hosts, and other infrastructure components. It then deploys Sitecore into this new VPC.
-
Deploy Sitecore into an existing VPC. This option provisions Sitecore in your existing AWS infrastructure.
The Partner Solution provides separate templates for these options. It also lets you configure Classless Inter-Domain Routing (CIDR) blocks, instance types, and Sitecore settings.
Predeployment steps
This Partner Solution requires that you sign up with Sitecore to obtain the Sitecore XP resource files.
-
Obtain a temporary Sitecore license or contact your Sitecore sales representative or Sitecore partner for a full Sitecore license.
-
Upload the license file to an S3 bucket into a prefix called
license. -
Extract the contents of the .zip file, but don’t extract any of the resulting .zip files. Using the same S3 bucket as the license file, upload these extracted files into a prefix called
resources. -
Create a certificate in Amazon Certificate Manager (ACM) for your Sitecore deployment in the Region where you deploy the Partner Solution. This certificate must be created as a wildcard certificate for your Sitecore domain (for example,
*.example.com).
This Partner Solution can optionally deploy a server for Apache Solr search. This Solr deployment, however, is a development server and not recommended for production use. It is therefore suggested that you provide a URL to your production Apache Solr search server or cluster when deploying this Partner Solution.
Deployment steps
-
Sign in to your AWS account, and launch this Partner Solution, as described under Deployment options. The AWS CloudFormation console opens with a prepopulated template.
-
Choose the correct AWS Region, and then choose Next.
-
On the Create stack page, keep the default setting for the template URL, and then choose Next.
-
On the Specify stack details page, change the stack name if needed. Review the parameters for the template. Provide values for the parameters that require input. For all other parameters, review the default settings and customize them as necessary. When you finish reviewing and customizing the parameters, choose Next.
Unless you’re customizing the Partner Solution templates or are instructed otherwise in this guide’s Predeployment section, don’t change the default settings for the following parameters: QSS3BucketName,QSS3BucketRegion, andQSS3KeyPrefix. Changing the values of these parameters will modify code references that point to the Amazon Simple Storage Service (Amazon S3) bucket name and key prefix. For more information, refer to the AWS Partner Solutions Contributor’s Guide. -
On the Configure stack options page, you can specify tags (key-value pairs) for resources in your stack and set advanced options. When you finish, choose Next.
-
On the Review page, review and confirm the template settings. Under Capabilities, select all of the check boxes to acknowledge that the template creates AWS Identity and Access Management (IAM) resources that might require the ability to automatically expand macros.
-
Choose Create stack. The stack takes about 1–1.5 hours to deploy.
-
Monitor the stack’s status, and when the status is CREATE_COMPLETE, the Sitecore XP deployment is ready.
-
To view the created resources, choose the Outputs tab.
Postdeployment steps
Create DNS entries
After deploying the Partner Solution, add DNS CNAME records to your internet-facing DNS for the Sitecore content delivery, content management, and identity servers.
These records correspond to the CDDNSName, CMDNSName, and ISDNSName deployment parameters. They point to the DNS name of the external facing ALB (ExternalALBDNS in the SitecoreStack deployment outputs).
If you deploy this Partner Solution into an existing VPC using a self-managed DNS, you must
create DNS CNAME entries for the Sitecore roles. The required CNAME host name and
corresponding load balancer DNS can be found in the outputs of RolesStack and SitecoreStack,
respectively. When it’s updated, log in to the instance that hosts the marketing automation
role, and start the Sitecore marketing automation Windows service.
Test the deployment
Use a web browser to find the DNS name you provided for the content delivery role.
To log in to Sitecore, retrieve the administrator password by opening AWS Secrets Manager from within the Region where you deployed this Partner Solution. Search for “sitecoreadmin” to find the password value.
When you have the password, use a web browser to find the DNS name for either the
content delivery role or content management role. Append /sitecore/admin to the DNS
name. This displays the login screen where you can log in and configure your Sitecore
environment.
Best practices for using Sitecore XP on AWS
Use AWS CloudFormation for ongoing management.
We recommend using the AWS CloudFormation console to manage updates and deletions for the resources that this Partner Solution creates. Use the Amazon EC2 console, AWS command line interface (CLI), or application programming interface (API) to change or delete resources created by this Partner Solution. Otherwise, future AWS CloudFormation operations on the stack may behave unexpectedly.
All Sitecore instances are in the private subnet, so there is no access to them from the internet. Both Amazon RDS and Amazon ElastiCache are accessible only from within the VPC and not from the internet. All traffic is routed to the Sitecore instances via the deployed load balancers.
Other useful information
Personalized content on Sitecore roles
Once the deployment of the Sitecore Partner Solution is complete, you have a default installation of Sitecore XP in your AWS account. Your custom Sitecore site must then be deployed to the Sitecore roles. Any media for your site (for example, pictures and videos) should be stored within an S3 bucket and referenced within the website’s code. Storing local media content through Sitecore roles should be avoided because it can increase the load on your content instances. It may also affect Auto Scaling because it takes time to transfer media to a new instance.
Parameter Store
All Sitecore role installations are done via the Sitecore Installation Framework (SIF). Using SIF allows parameters to be passed to the Sitecore role installation when the instance starts for the first time. These parameters are stored in AWS Systems Manager Parameter Store. If any of these parameter values in Parameter Store are updated, the instances can be deleted so that when the instance starts up, the Sitecore installation uses the updated parameter values. For example, this could be used to update the Solr URL or Solr Core prefix for the Sitecore roles.
Secrets Manager
All Sitecore passwords are generated via AWS Secrets Manager. They are referenced when the databases are created and the Sitecore roles are installed.
Sitecore certificates
Because Sitecore requires Secure Sockets Layer (SSL) communication between roles, an internal self-signed certificate is generated. This certificate is imported into the certificate store on the Sitecore AMI and then exported and stored in the S3 bucket provided in the deployment parameters. The certificate is then converted and imported into ACM via a Lambda function and used on the internal Application Load Balancer for the HTTPS listener. All other internal Sitecore roles sit behind their own Network Load Balancers because they require TLS pass-through.
The certificate is valid for five years from the date of installation. Should a new certificate be
needed for the Sitecore deployment, one can be generated by running the sc-newcerts.ps1 script, which can be found in the C:\quickstart\scripts folder. When it’s
generated, the certificate must be converted, imported into ACM, and updated on the
internal Application Load Balancer listener.
Sitecore Internet Information Service configurations
Because Sitecore is a database- and personalization-driven CMS, the Sitecore Internet
Information Service (IIS) must be configured for preloaded content, and the application
pool must always be running. When you install a Sitecore role, the corresponding
application pool is set to AlwaysRunning and the website is set to preload content.
Redis for session management
While the content delivery role installs, the Sitecore configuration files update for both private- and shared-session management. If these files are overwritten by custom content, they must be updated with the correct Redis details.
The URL for Redis can be found in the CloudFormation outputs, or in the SSM Parameter Store.
Troubleshooting
For troubleshooting common Partner Solution issues visit the AWS Partner Solution General Content Guide or the Troubleshooting CloudFormation page in the AWS documentation.
Q. I encountered a CREATE_FAILED error when I launched the Partner Solution.
A. If AWS CloudFormation fails to create the stack, we recommend that you relaunch the template with Rollback on failure set to No. (This setting is under Advanced in the AWS CloudFormation console, Options page.) With this setting, the stack’s state is retained and the instance is left running, so you can troubleshoot the issue. (For Windows, look at the log files in %ProgramFiles%\Amazon\EC2ConfigService and C:\cfn\log.)
| When you set Rollback on failure to Disabled, you continue to incur AWS charges for this stack. Please make sure to delete the stack when you finish troubleshooting. |
For additional information, see Troubleshooting AWS CloudFormation on the AWS website.
Q. I encountered a size limitation error when I deployed the AWS CloudFormation templates.
A. We recommend that you launch the Partner Solution templates from the links in this guide or from another S3 bucket. If you deploy the templates from a local copy on your computer or from a location other than an S3 bucket, you might encounter template size limitations. For more information about AWS CloudFormation quotas, see the AWS documentation.
Q. When browsing the content-delivery website, I get a 504 error.
A. This issue is experienced if the content-delivery or content-management server takes more than 60 seconds to respond to an Application Load Balancer request. Ensure that the Sitecore role has the IIS Application Pool configured to remain running. Based on the complexity of your website, responses from the database and other roles can also affect response time. Ensure that the database and instances are sized correctly for your environment.
Using browser caching or a content delivery network can also assist the caching of common content and therefore reduce the load on the Sitecore environment.
Q. When I try to log in to the Sitecore administrator interface, I get an incorrect password error.
A. Despite installation logs that show the password was correctly configured, there are known issues where the specified Sitecore administrator password in AWS Secrets Manager is not successfully applied. To log in, you must reset the password in the Sitecore Core database.
Q. How do I update SSL certificates when they expire?
A. Refer to the Other useful information section of this guide.
Q. Where are the deployment logs?
A. All resources and logs for deployments are found either in Amazon CloudWatch Logs or
in the instances themselves under C:\resources\logs\.
Q. How do I apply a new license?
A. When a Sitecore license expires, manually update it for each instance by copying your
Sitecore license.xml file to the /site/wwwroot/App_Data directory. But, if an Auto Scaling
group creates a new instance, it attempts to retrieve the Sitecore license from the S3 bucket
and prefix provided in the initial deployment. Therefore, it’s necessary to replace the
existing license by uploading a new Sitecore license into the S3 bucket and prefix.
Customer responsibility
After you deploy a Partner Solution, confirm that your resources and services are updated and configured—including any required patches—to meet your security and other needs. For more information, refer to the Shared Responsibility Model.
Feedback
To submit feature ideas and report bugs, use the Issues section of the GitHub repository for this Partner Solution. To submit code, refer to the Partner Solution Contributor’s Guide. To submit feedback on this deployment guide, use the following GitHub links:
Notices
This document is provided for informational purposes only. It represents current AWS product offerings and practices as of the date of issue of this document, which are subject to change without notice. Customers are responsible for making their own independent assessment of the information in this document and any use of AWS products or services, each of which is provided "as is" without warranty of any kind, whether expressed or implied. This document does not create any warranties, representations, contractual commitments, conditions, or assurances from AWS, its affiliates, suppliers, or licensors. The responsibilities and liabilities of AWS to its customers are controlled by AWS agreements, and this document is not part of, nor does it modify, any agreement between AWS and its customers.
The software included with this paper is licensed under the Apache License, version 2.0 (the "License"). You may not use this file except in compliance with the License. A copy of the License is located at https://aws.amazon.com/apache2.0/ or in the accompanying "license" file. This code is distributed on an "as is" basis, without warranties or conditions of any kind, either expressed or implied. Refer to the License for specific language governing permissions and limitations.