Boomi Molecule on AWS
Partner Solution Deployment Guide

July 2022
Ryan Vanderwerf - Partner Solutions Architect, Sean Williams - Partner Solutions Architect
Andrew Glenn - AWS Integration and Automation team, Dave May - AWS Integration and Automation team

| Refer to the GitHub repository to view source files, report bugs, submit feature ideas, and post feedback about this Partner Solution. To comment on the documentation, refer to Feedback. |
This Partner Solution was created by Boomi in collaboration with Amazon Web Services (AWS). Partner Solutions are automated reference deployments that help people deploy popular technologies on AWS according to AWS best practices. If you’re unfamiliar with AWS Partner Solutions, refer to the AWS Partner Solution General Information Guide.
Overview
This Quick Start deploys Boomi Molecule on the AWS Cloud. This guide covers the steps necessary to deploy this Quick Start.
This Quick Start is for users who are looking for an integration platform as a service (iPaaS) that can be hosted on AWS. This Quick Start enables you to deploy a Boomi Molecule cluster on AWS and administer it through the Boomi AtomSphere platform.
Costs and licenses
This deployment requires a Boomi Molecule Enterprise license.
There is no cost to use this Quick Start, but you will be billed for any AWS services or resources that this Quick Start deploys. For more information, refer to the AWS Quick Start General Information Guide.
Architecture
Deploying this Quick Start with default parameters builds the following Boomi Molecule environment in the AWS Cloud.
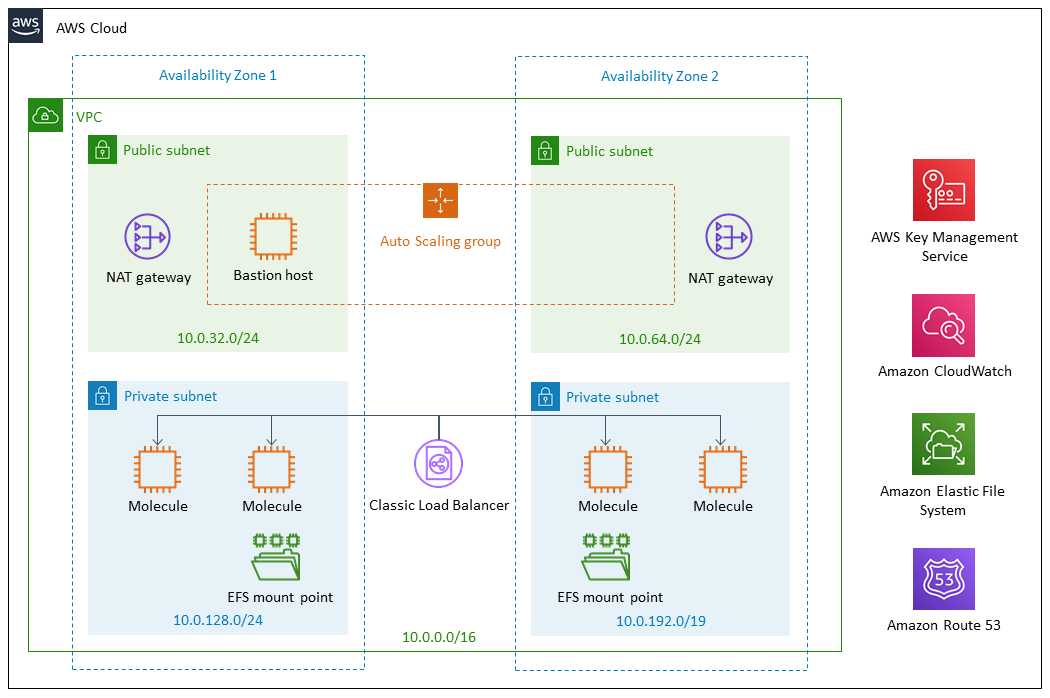
As shown in Figure 1, this Quick Start sets up the following:
-
A highly available architecture that spans two Availability Zones.*
-
A virtual private cloud (VPC) configured with public and private subnets according to AWS best practices, to provide you with your own virtual network on AWS.*
-
In the public subnets:
-
Managed network address translation (NAT) gateways to allow outbound internet access for resources in the private subnets.*
-
A Linux bastion host in an Auto Scaling group to allow inbound Secure Shell (SSH) access to Amazon Elastic Compute Cloud (Amazon EC2) instances in public and private subnets, with Amazon CloudWatch for monitoring.*
-
-
An Application Load Balancer to route traffic to the Boomi Molecule instances in the private subnets.
-
In the private subnets:
-
Boomi Molecule deployed to four Amazon EC2 instances.
-
Amazon Elastic File System (Amazon EFS) mount points.
-
-
An Amazon CloudWatch alarm to monitor EC2 instances and initiate recovery actions if an instance fails.
* The template that deploys this Quick Start into an existing VPC skips the components marked by asterisks and prompts you for your existing VPC configuration.
Deployment options
This Quick Start provides the following deployment options:
-
Deploy Boomi Molecule into a new VPC. This option builds a new AWS environment that consists of the VPC, subnets, NAT gateways, security groups, bastion hosts, and other infrastructure components. It then deploys Boomi Molecule into this new VPC.
-
Deploy Boomi Molecule into an existing VPC. This option provisions Boomi Molecule in your existing AWS infrastructure.
This Quick Start provides separate templates for these options. It also lets you configure Classless Inter-Domain Routing (CIDR) blocks, instance types, and Boomi Molecule settings.
Predeployment steps
Prepare your Boomi account
Ensure that your Boomi account has at least one available Enterprise Molecule license. Ensure that you have a valid account ID, installation token, and API Key or username and password.
Deployment steps
-
Sign in to your AWS account, and launch this Partner Solution, as described under Deployment options. The AWS CloudFormation console opens with a prepopulated template.
-
Choose the correct AWS Region, and then choose Next.
-
On the Create stack page, keep the default setting for the template URL, and then choose Next.
-
On the Specify stack details page, change the stack name if needed. Review the parameters for the template. Provide values for the parameters that require input. For all other parameters, review the default settings and customize them as necessary. When you finish reviewing and customizing the parameters, choose Next.
Unless you’re customizing the Partner Solution templates or are instructed otherwise in this guide’s Predeployment section, don’t change the default settings for the following parameters: QSS3BucketName,QSS3BucketRegion, andQSS3KeyPrefix. Changing the values of these parameters will modify code references that point to the Amazon Simple Storage Service (Amazon S3) bucket name and key prefix. For more information, refer to the AWS Partner Solutions Contributor’s Guide. -
On the Configure stack options page, you can specify tags (key-value pairs) for resources in your stack and set advanced options. When you finish, choose Next.
-
On the Review page, review and confirm the template settings. Under Capabilities, select all of the check boxes to acknowledge that the template creates AWS Identity and Access Management (IAM) resources that might require the ability to automatically expand macros.
-
Choose Create stack. The stack takes about 1 hour to deploy.
-
Monitor the stack’s status, and when the status is CREATE_COMPLETE, the Boomi Molecule deployment is ready.
-
To view the created resources, choose the Outputs tab.
Postdeployment steps
Test the deployment
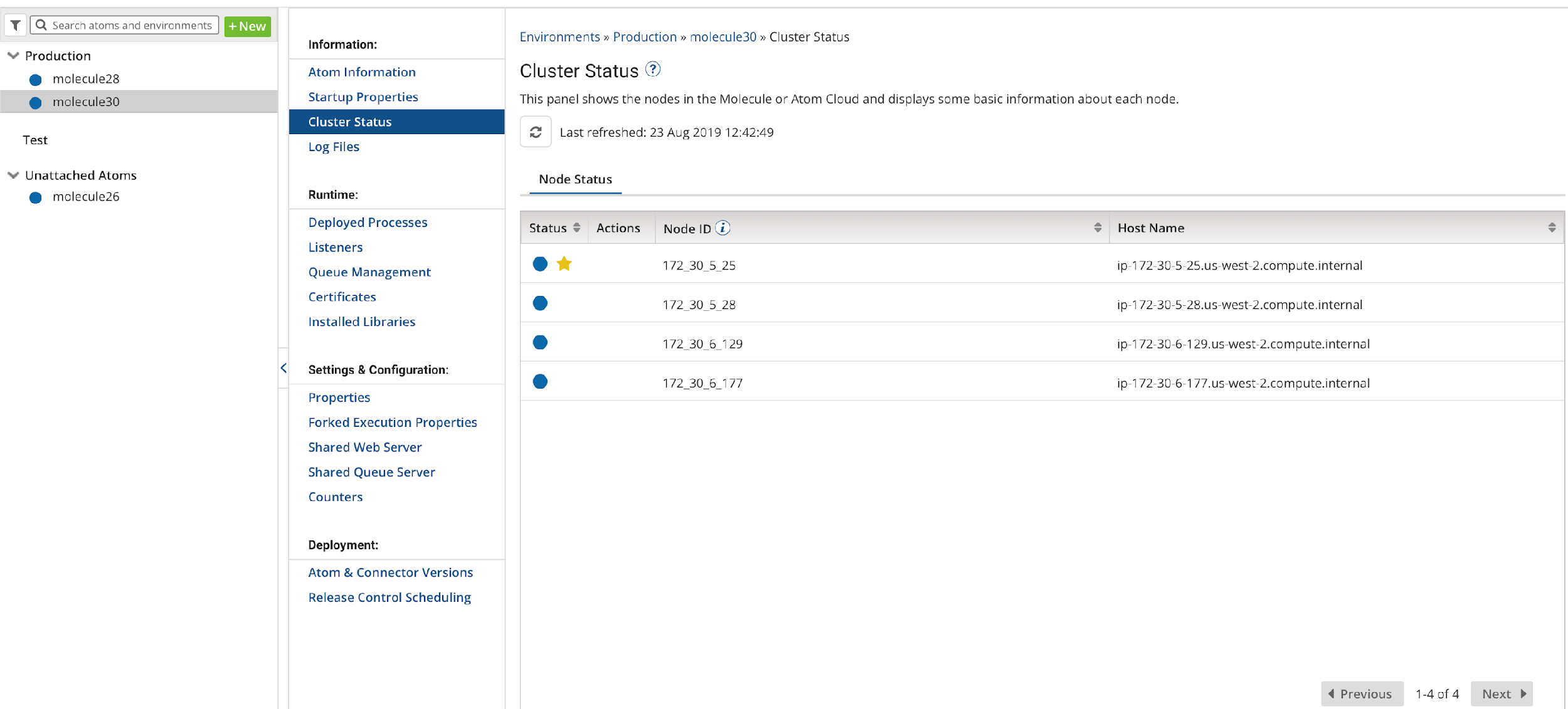
To view the Molecule on Boomi AtomSphere, log in to your Boomi account. On the Manage, choose Atom Management. The newly created Amazon EC2 instance Molecule cluster is displayed.
Boomi dashboard with an unattached AWS-managed Molecule cluster
You can attach Molecules to any environment you have staged and deploy workloads to that Molecule cluster. On the Boomi dashboard, your deployed Molecule is under Unattached Atoms. For more information, refer to Attaching an Atom to or detaching an Atom from an environment.
Security
This Quick Start deploys a bastion host and a Boomi Molecule cluster into an AWS VPC. The bastion host is the only means of accessing the Boomi Molecule cluster at a command-line level. The Boomi Molecule cluster is deployed into private subnets and cannot be reached through the internet. The Boomi Molecule cluster communicates through a NAT Gateway for updates and patches, and it communicates through the public-facing Application Load Balancer to communicate with the Boomi AtomSphere platform.
Performance monitoring
Monitoring the CPU, network, and Amazon Elastic Block Store (Amazon EBS) performance of your AWS Boomi Molecule cluster is done through CloudWatch metrics.
CPU and network performance are measured in utilization, network in and out, network packets in and out, and system status checks.
Amazon EBS volume performance is measured in read and write throughput, average read and write size, read and write bandwidth, read and write latency, and volume idle time.
Amazon EFS reports metrics to CloudWatch and can be monitored there. Metrics include client connections, data read and data write bytes, and IO percent limits.
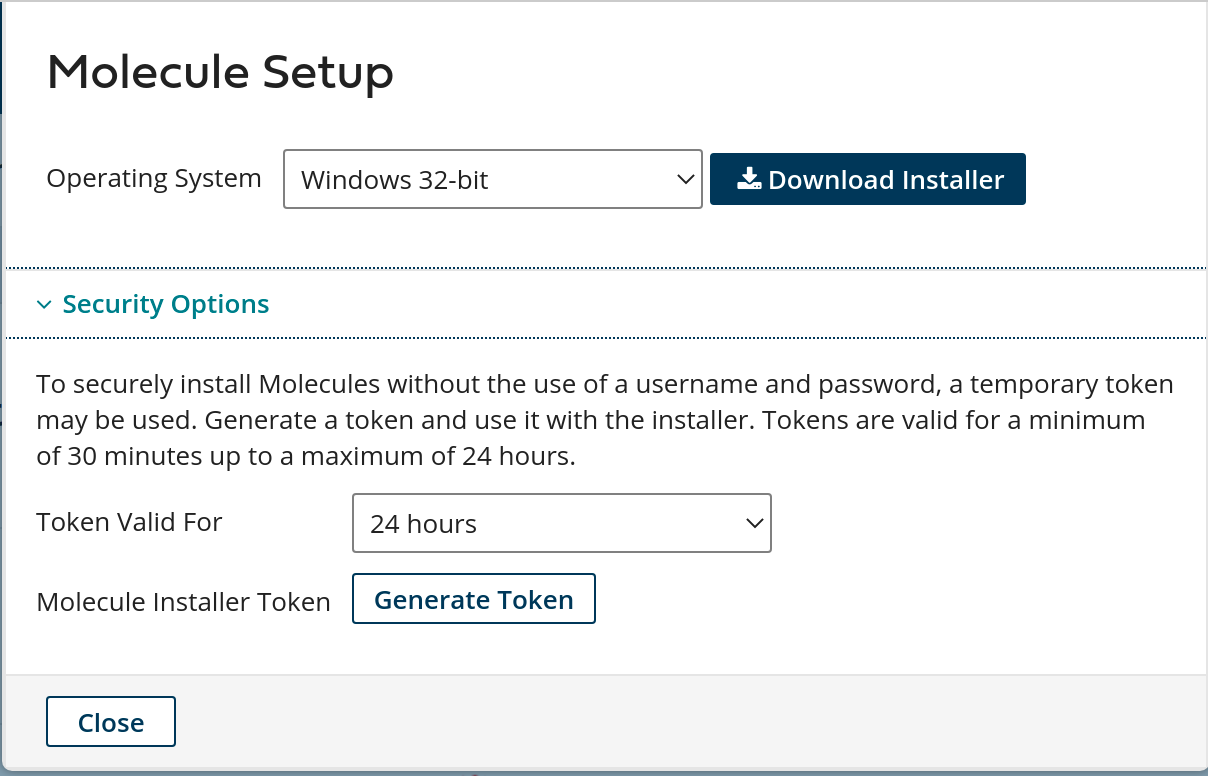
Creating an installation token
Administrators can create an installation token without having to share login credentials for an Atom/Molecule installation. To create an installation token, do the following:
-
On the Manage menu, choose Atom Management.
-
Choose New, Molecule.
-
On the Build page, choose the Welcome tab.
-
Under the Create heading, choose Molecule.
-
Choose Security Options.
-
In the Token Valid for field, select the length of time the token is valid (30 minutes to 24 hours).
-
Click Generate Token.
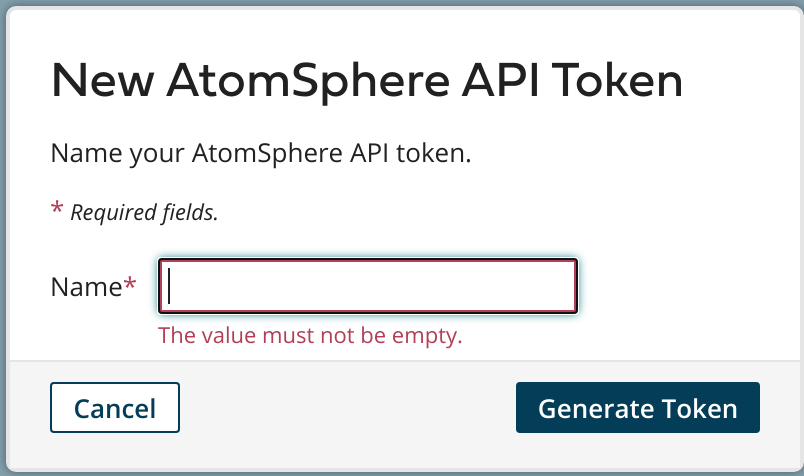
Creating an API token
Administrators can create a long-lived API token without having to share login credentials for an Atom/Molecule installation. To create an user API token, do the following:
-
On the Settings menu, choose Account Information and Setup.
-
Choose the AtomSphere API Tokens tab.
-
Choose Add New Token.
-
Enter a unique name for the token.
-
Choose Generate Token.
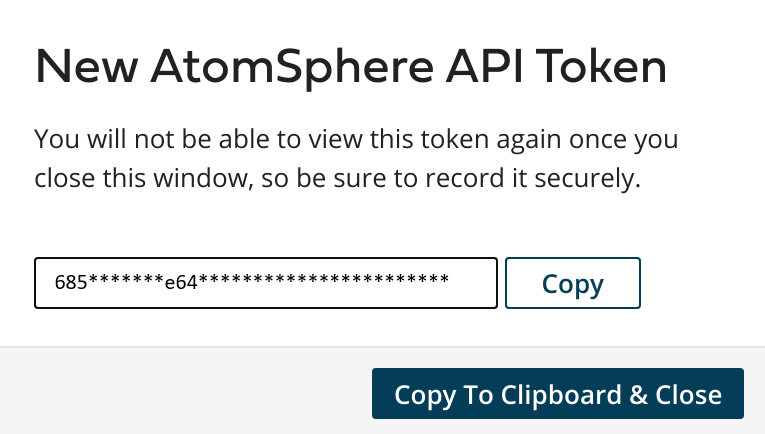
-
Choose Copy to copy the token string to the clipboard without exiting. When you are ready to exit, click Copy to Clipboard & Close to copy the token string and exit the dialog.
Copy the token key value to a secure location. It is recommended that you treat tokens with the same level of security as you would a password. If you lose it, you will have to generate a new token and revoke the old one.
Troubleshooting
For troubleshooting common Quick Start issues, refer to the AWS Quick Start General Information Guide and Troubleshooting CloudFormation.
Customer responsibility
After you deploy a Partner Solution, confirm that your resources and services are updated and configured—including any required patches—to meet your security and other needs. For more information, refer to the Shared Responsibility Model.
Feedback
To submit feature ideas and report bugs, use the Issues section of the GitHub repository for this Partner Solution. To submit code, refer to the Partner Solution Contributor’s Guide. To submit feedback on this deployment guide, use the following GitHub links:
Notices
This document is provided for informational purposes only. It represents current AWS product offerings and practices as of the date of issue of this document, which are subject to change without notice. Customers are responsible for making their own independent assessment of the information in this document and any use of AWS products or services, each of which is provided "as is" without warranty of any kind, whether expressed or implied. This document does not create any warranties, representations, contractual commitments, conditions, or assurances from AWS, its affiliates, suppliers, or licensors. The responsibilities and liabilities of AWS to its customers are controlled by AWS agreements, and this document is not part of, nor does it modify, any agreement between AWS and its customers.
The software included with this paper is licensed under the Apache License, version 2.0 (the "License"). You may not use this file except in compliance with the License. A copy of the License is located at https://aws.amazon.com/apache2.0/ or in the accompanying "license" file. This code is distributed on an "as is" basis, without warranties or conditions of any kind, either expressed or implied. Refer to the License for specific language governing permissions and limitations.