Trend Micro Deep Security on AWS
Partner Solution Deployment Guide

May 2022
Trend Micro
Tony Bulding, AWS Integration & Automation team

| Refer to the GitHub repository to view source files, report bugs, submit feature ideas, and post feedback about this Partner Solution. To comment on the documentation, refer to Feedback. |
This Partner Solution was created by Trend Micro in collaboration with Amazon Web Services (AWS). Partner Solutions are automated reference deployments that help people deploy popular technologies on AWS according to AWS best practices. If you’re unfamiliar with AWS Partner Solutions, refer to the AWS Partner Solution General Information Guide.
Overview
This Partner Solution deploys Trend Micro Deep Security to the AWS Cloud. If you are unfamiliar with AWS Partner Solutions, see the AWS Partner Solution General Information Guide. For more information about Deep Security, refer to Deep Security Software.
This guide covers how to deploy Trend Micro Deep Security using the supplied templates. It does not cover other aspects of administering Deep Security. For more information about administering Deep Security, refer to the Trend Micro Deep Security Help Center.
Costs and licenses
There is no cost to use this Partner Solution, but you will be billed for any AWS services or resources that this Partner Solution deploys. For more information, refer to the AWS Partner Solution General Information Guide.
You must have a license for Trend Micro Deep Security before you launch this Partner Solution. For more information, refer to the Predeployment section of this guide.
Architecture
Deploying this Partner Solution with default parameters builds the following Deep Security environment in the AWS Cloud.
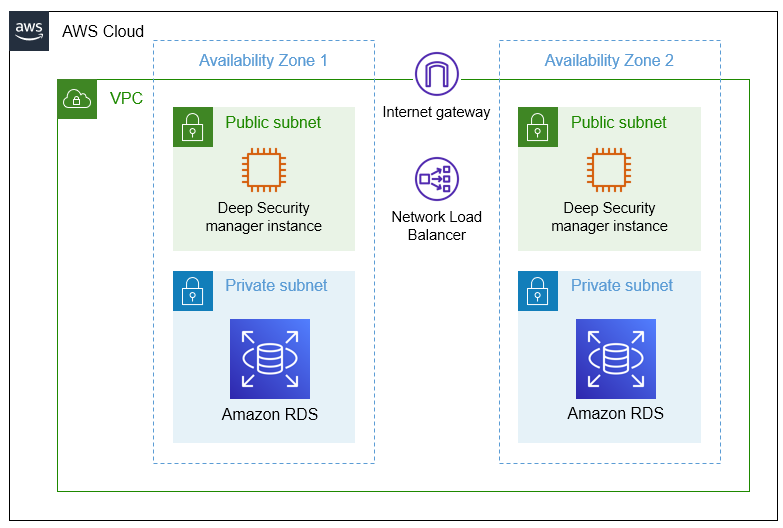
As shown in Figure 1, this Partner Solution sets up the following:
-
A highly available architecture that spans two Availability Zones.*
-
A virtual private cloud (VPC) configured with public and private subnets, according to AWS best practices, to provide you with your own virtual network on AWS.*
-
An internet gateway that connects the VPC to the internet.
-
In the public subnets:
-
Amazon Elastic Compute Cloud (Amazon EC2) instances for Deep Security Manager.
-
Elastic Load Balancing that distributes incoming traffic across the Amazon EC2 instances (not shown).
-
-
In the private subnets:
-
Amazon Relational Database Service (Amazon RDS) to set up, operate, and scale a relational database.
-
* The template that deploys this Partner Solution into an existing VPC skips the components marked by asterisks and prompts you for your existing VPC configuration.
Deployment options
This Partner Solution provides the following deployment options:
-
Deploy Deep Security (Per Protected Instance Hour) into an existing VPC. This option provisions Deep Security in your existing AWS infrastructure.
-
Deploy Deep Security (Bring Your Own License) into an existing VPC. This option provisions Deep Security in your existing AWS infrastructure.
This Partner Solution provides the following AWS GovCloud deployment options:
-
Deploy Deep Security (Per Protected Instance Hour) into an existing VPC. This option provisions Deep Security in your existing AWS infrastructure.
-
Deploy Deep Security (Bring Your Own License) into an existing VPC. This option provisions Deep Security in your existing AWS infrastructure.
Predeployment steps
Subscribe to Trend Micro Deep Security
Before you launch this Partner Solution, subscribe to the Amazon Machine Image (AMI) from AWS Marketplace for Trend Micro Deep Security.
The following licensing options are available:
-
Per Protected Instance Hour: A consumption-based option that allows you to pay hourly per protected instance. Your costs are determined by the number of instances you protect per hour. For current prices, refer to Pricing Information.
-
Bring Your Own License (BYOL): A perpetual license for organizations that prefer traditional procurement. For more information, contact aws@trendmicro.com.
|
Deployment steps
-
Sign in to your AWS account, and launch this Partner Solution, as described under Deployment options. The AWS CloudFormation console opens with a prepopulated template.
-
Choose the correct AWS Region, and then choose Next.
-
On the Create stack page, keep the default setting for the template URL, and then choose Next.
-
On the Specify stack details page, change the stack name if needed. Review the parameters for the template. Provide values for the parameters that require input. For all other parameters, review the default settings and customize them as necessary. When you finish reviewing and customizing the parameters, choose Next.
Unless you’re customizing the Partner Solution templates or are instructed otherwise in this guide’s Predeployment section, don’t change the default settings for the following parameters: QSS3BucketName,QSS3BucketRegion, andQSS3KeyPrefix. Changing the values of these parameters will modify code references that point to the Amazon Simple Storage Service (Amazon S3) bucket name and key prefix. For more information, refer to the AWS Partner Solutions Contributor’s Guide. -
On the Configure stack options page, you can specify tags (key-value pairs) for resources in your stack and set advanced options. When you finish, choose Next.
-
On the Review page, review and confirm the template settings. Under Capabilities, select all of the check boxes to acknowledge that the template creates AWS Identity and Access Management (IAM) resources that might require the ability to automatically expand macros.
-
Choose Create stack. The stack takes about 1 hour to deploy.
-
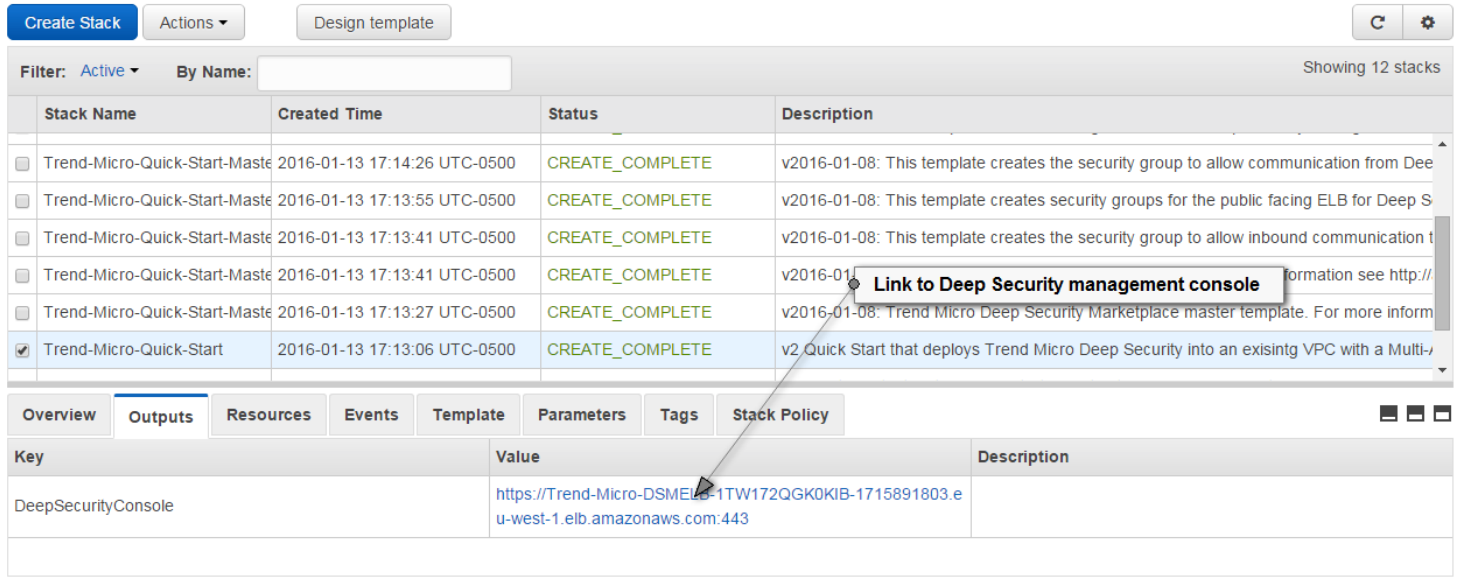
Monitor the stack’s status, and when the status is CREATE_COMPLETE, the Trend Micro Deep Security deployment is ready.
-
To view the created resources, choose the Outputs tab.
Postdeployment steps
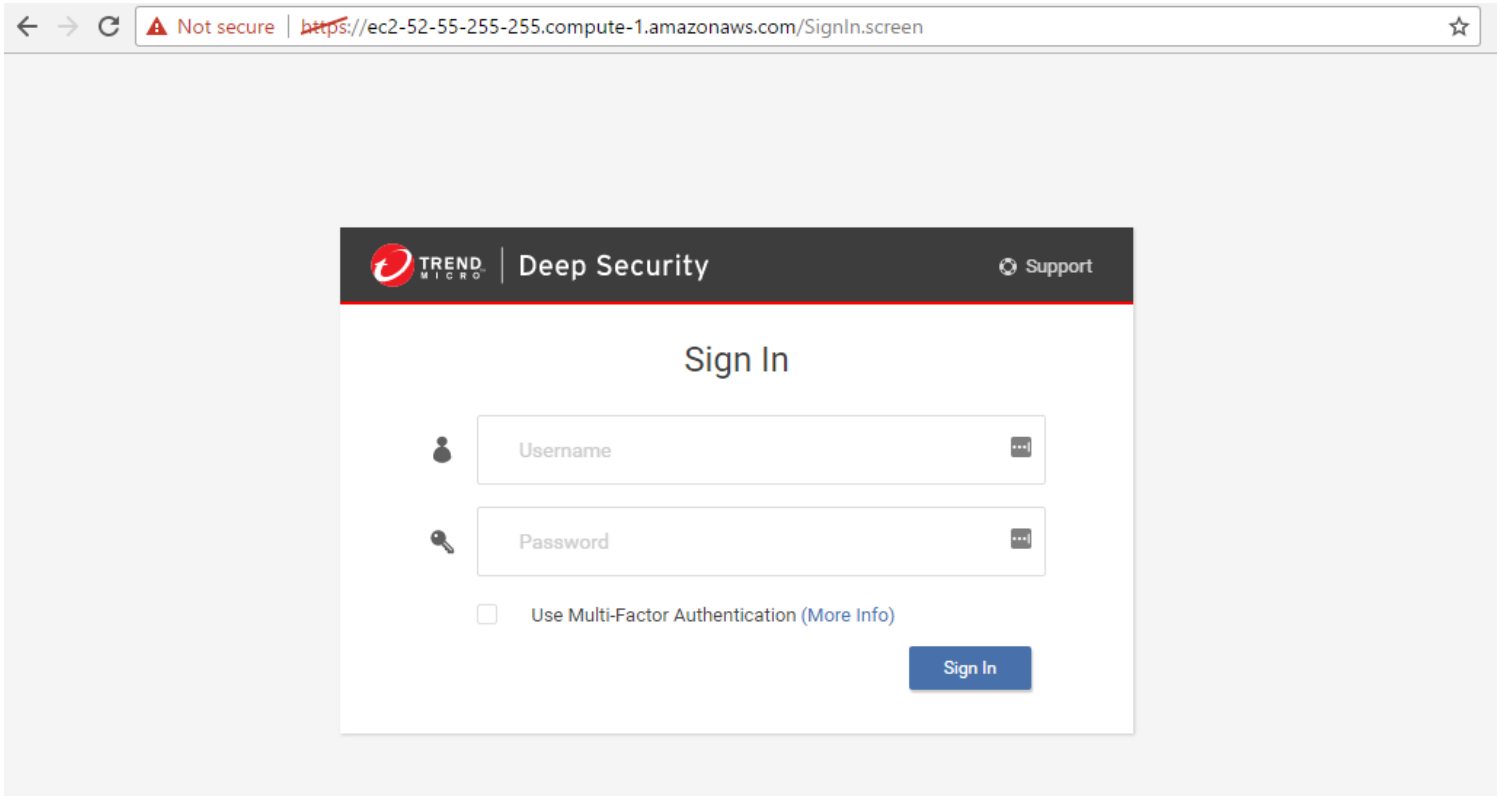
Log in to the Deep Security Manager console
Navigate to the Outputs tab of the AWS CloudFormation stack, which provides a URL to the Deep Security Manager interface. Choose this link and log in using the user name and password you supplied during the launch of the template.
Elastic Load Balancing certificate
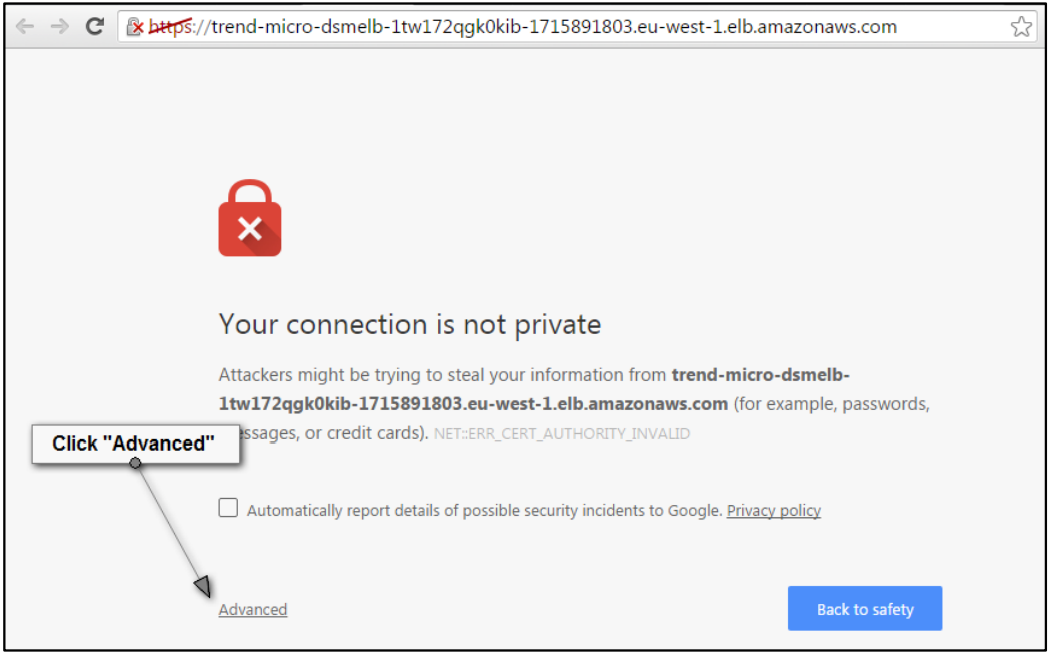
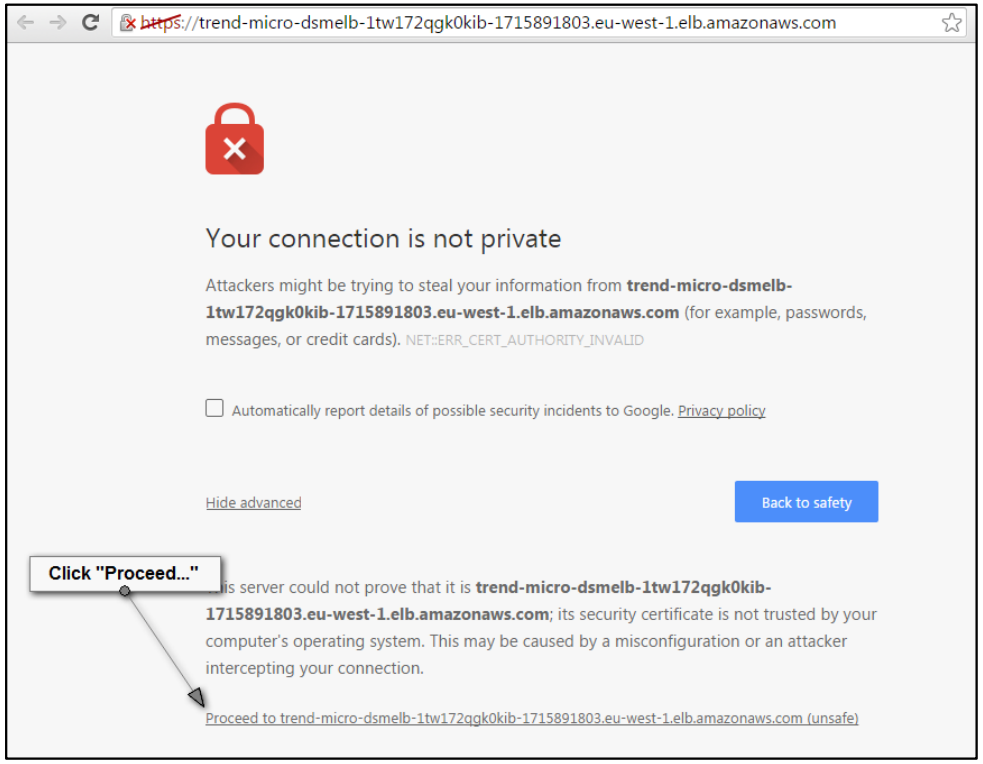
Elastic Load Balancing for Deep Security Manager is initially configured to use a self-signed certificate for HTTPS connections. Your browser may give you an error when you try to access the console. If you update the Elastic Load Balancing certificate, you can then proceed to the Deep Security Manager console.
Deep Security runs as part of your core infrastructure. As a result, its attack surface should be minimized. This Partner Solution helps reduce this attack service by:
-
Using security groups to restrict traffic.
-
Deploying a Deep Security Agent on the Manager instance.
-
Using role-based access controls within the platform to help ensure that only valid users have access to the platform.
The Deep Security Manager is initially configured to use a public load balancer so it can protect instances in AWS Regions and AWS accounts outside of where it is deployed. If you don’t require this functionality and don’t require the Deep Security Manager console to be accessible from the internet, reconfigure Deep Security Manager to use a private load balancer to further reduce the attack surface. If you want to use a private load balancer and still protect instances outside the VPC where Deep Security Manager is deployed, refer to Connect VPCs using VPC peering.
If you are using the Partner Solution as the basis of a production deployment and not as a proof of concept, update the self-signed certificate to a certificate that is signed by a trusted certificate authority.
To obtain a signed certificate, you are required by the certificate authority to specify a formal subdomain (for example, deepsecurityconsole.mycompany.com) and use this to access the Deep Security load balancer.
|
To update the security certificate of the load balancer, follow these steps:
-
Register the domain name that you use to access the Deep Security Manager console.
-
Obtain a certificate for this domain from a trusted certificate authority.
-
Add the certificate to your certificate store. For more information, refer to Managing server certificates in IAM.
-
Update the DNS settings of the load balancer to use the new domain name. For more information, refer to Configure a custom domain name for your Classic Load Balancer.
-
Replace the SSL certificate of the load balancer. For more information, refer to Configure a custom domain name for your Classic Load Balancer.
Troubleshooting
For troubleshooting common Partner Solution issues, see the AWS Partner Solution General Information Guide and Troubleshooting CloudFormation.
Customer responsibility
After you deploy a Partner Solution, confirm that your resources and services are updated and configured—including any required patches—to meet your security and other needs. For more information, refer to the Shared Responsibility Model.
Feedback
To submit feature ideas and report bugs, use the Issues section of the GitHub repository for this Partner Solution. To submit code, refer to the Partner Solution Contributor’s Guide. To submit feedback on this deployment guide, use the following GitHub links:
Notices
This document is provided for informational purposes only. It represents current AWS product offerings and practices as of the date of issue of this document, which are subject to change without notice. Customers are responsible for making their own independent assessment of the information in this document and any use of AWS products or services, each of which is provided "as is" without warranty of any kind, whether expressed or implied. This document does not create any warranties, representations, contractual commitments, conditions, or assurances from AWS, its affiliates, suppliers, or licensors. The responsibilities and liabilities of AWS to its customers are controlled by AWS agreements, and this document is not part of, nor does it modify, any agreement between AWS and its customers.
The software included with this paper is licensed under the Apache License, version 2.0 (the "License"). You may not use this file except in compliance with the License. A copy of the License is located at https://aws.amazon.com/apache2.0/ or in the accompanying "license" file. This code is distributed on an "as is" basis, without warranties or conditions of any kind, either expressed or implied. Refer to the License for specific language governing permissions and limitations.